COOKIE COOKIE GIVE ME A COOKIE
A trail of internet crumbs you can sweep up in five minutes
My father, Mikhael Kollander, was a massive polymath. Musician, inventor, contractor, songwriter. He reinvented himself nine times. But at his core he was a guitarist and a composer. Before he built houses in Los Angeles, before he became a general contractor, he was a musician. Capitol Records. The Fifth Dimension. Bobby Darin’s world tour. Session work across the LA studio circuit in the late 1960s.
One of the acts he played guitar for was Andy Williams. The “It’s the Most Wonderful Time of the Year” guy. The guy who defined American Christmas, before Mariah Carey rightfully ascended the throne. In the 1960s, The Andy Williams Show was one of the biggest variety programs on television. NBC. Prime time. Tens of millions of viewers every week.
In 1969, the show introduced a recurring character called Cookie Bear. A guy in a bear costume who walked onstage, begged for cookies, and never got any. Poor Cookie Bear. Fans loved him so much they started mailing mountains of baked goods to the actor. Meanwhile every week, Andy screamed at him: “NO COOKIES! NOT NOW, NOT EVER!” And slammed the door in his face.
If only we had that level of agency in our privacy choices today.
That same year, students at Brown University started manually sending messages to other people’s computer terminals, freezing them and demanding cookies. The idea spread to MIT, where a programmer named C.D. Tavares decided to automate it. He wrote a program for Multics, an early operating system that ran on machines that filled entire rooms. The terminals were electric typewriters. No screen. Just paper rolling through a carriage. Characters printed at about 15 per second. Chunka chunka chunk.
His program printed the word COOKIE on your terminal. Then faster: COOKIE COOKIE GIVE ME A COOKIE. The only way to make it stop was to type “cookie.” What made it particularly nasty was a trick with the operating system’s alarm timer: the program could put itself to sleep and wake back up later. When you searched for it, it wasn’t running. It was hiding. Waiting. Then it came back. He named it after Cookie Bear from The Andy Williams Show.
Not Sesame Street.
Sesame Street had barely aired its first episode. But over the decades, Sesame Street’s Cookie Monster became the cultural reference that stuck with my fellow developer and cybersecurity nerds. But it actually started with a bear costume and my dad’s guitar :)
Tavares’s program spread to every computer running that system in the world. Including a classified installation in the Pentagon. The Pentagon knew about it. They couldn’t stop it either. It was the world’s first malware.
Today, the word “cookie” still lives in computing. Different meaning, same appetite. Except now the things that want your cookies aren’t wearing bear costumes. They’re services that auction your data to advertisers in less than a second, and criminal operations that steal it at industrial scale. Both businesses. Both profiting off you. One is legal. One isn’t. Neither asked.
Imagine you’re five years old. There’s a kid at school. Not your friend. The annoying one. The one who follows you around writing everything in a little notebook. Swings: three minutes. Slide: the twisty one… twice. Apple juice (not the orange). Farted during circle time and tried to pretend it didn’t happen. All in the notebook.
Now imagine fifty of those kids. Following you everywhere. Every playground. Every day. For two years. And they all share notebooks.
And then you go to the other place. The one you don’t tell anyone about. Everyone has one. Even grown-ups. Especially grown-ups. ;)
The fifty kids follow you there too. That’s what happens when you click “Accept All Cookies.” And even when you click “Reject All,” nearly half of them keep following you anyway.
But it gets worse. The playground itself has cameras. Built into the swings. Built into the slide. Already recording before anyone asked. You agreed to them when your parents signed you up. It was in the tiny writing nobody reads. That’s what your phone apps do. Instagram. TikTok. They don’t ask about cookies. They don’t need to. The whole playground is theirs. And those cameras see everything the kids with notebooks see, plus a whole lot more.
The cookie banner on almost every website releases dozens of tracking programs the moment you click it. Behind the banner is a company called a consent management platform. OneTrust and Cookiebot are the biggest ones. They handle the banner for the website. On CNN it says “Agree.” On Delta Airlines, “I understand.” The language is vague. The machinery isn’t.
When you click, the platform generates something called a TC String under the advertising industry’s consent framework. It looks like random characters. It’s a compressed permission slip that encodes your “yes” for over 1,200 individual advertising companies, one bit per company. One click. A thousand companies you’ve never heard of now have permission to follow you around.
Within about half a second, Google places a tracking file on your device that identifies you for 400 days. Meta (the company that owns Instagram and Facebook) places one through a tracking pixel. That’s a tiny invisible image embedded in the page’s code. One pixel by one pixel. Invisible without developer tools. Meta’s pixel sits on roughly half the websites in the S&P 500 and a third of healthcare websites. These pixels start collecting before you even touch the banner.
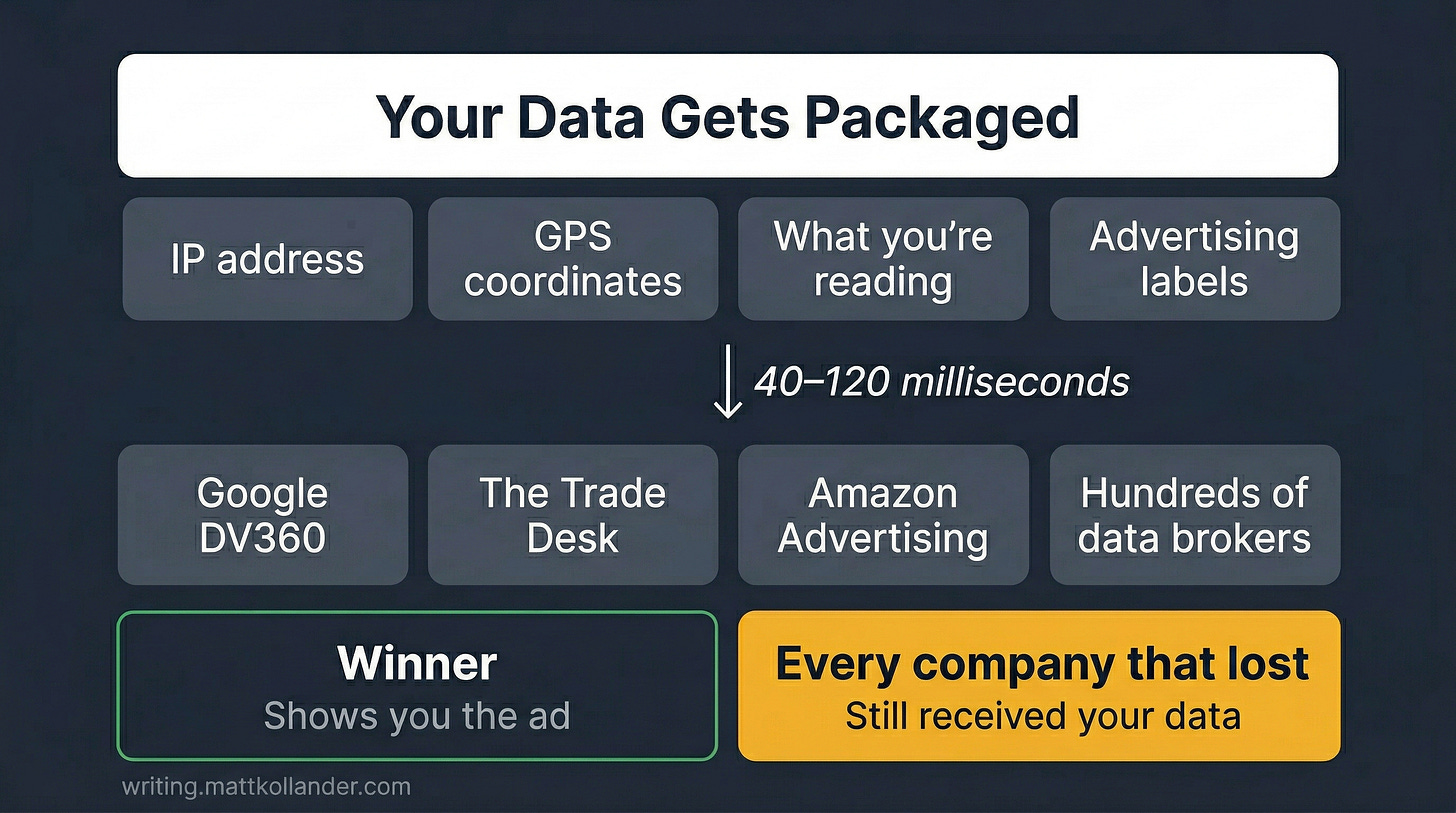
Then an auction starts. Before the page finishes loading, an ad exchange packages your data and broadcasts it to dozens of companies bidding on the right to show you an ad. Google’s DV360, The Trade Desk, Amazon Advertising, and hundreds of smaller data brokers all receive your IP address, your GPS coordinates, what you’re reading, and your browsing history sliced into advertising labels: health conditions you’ve researched, financial stress signals, dating activity, and yes, those late-night searches you’d rather not explain to your boyfriend, wife, parents, or boss. ;) The auction completes in 40 to 120 milliseconds. Even the companies that lost the auction still received your data.
That’s what happens on a website. But the cookie banner only covers part of your day.
About 62% of all web traffic is on phones and tablets. And 88% of the time people spend on their phones is in apps, not browsers. Instagram. TikTok. YouTube. Those apps don’t show you a cookie banner. They don’t need to. Cookies are a browser technology. Apps track you through something different and worse.
Each app contains roughly 18 embedded tracking programs from third-party companies, baked directly into the app’s code. Google’s Firebase is embedded in virtually every Android app that tracks user behavior. Meta’s tracking code is in roughly 20% of iOS apps. These programs access things cookies never could: your precise GPS coordinates, your accelerometer data (how you hold and move your phone), your battery level, which other apps you have installed, your network operator. Dancing. Cooking. Pooping. “Working out.” Your phone is always in your pocket. The accelerometer data alone tells a fascinating story of your life. That’s how Instagram seems to know what you talked about at dinner. It doesn’t need to listen through your microphone. It has enough data about your behavior and your device to figure it out.
Every video you watch, how long you watch, whether you pause, how fast you scroll past. The apps are free because you’re not the customer. You’re the product. The advertisers are the customers. Your identity, your habits, your browsing patterns are what’s being sold. Not the cute cat videos you fall asleep to. And not the other videos you watch when you can’t sleep, either ;)
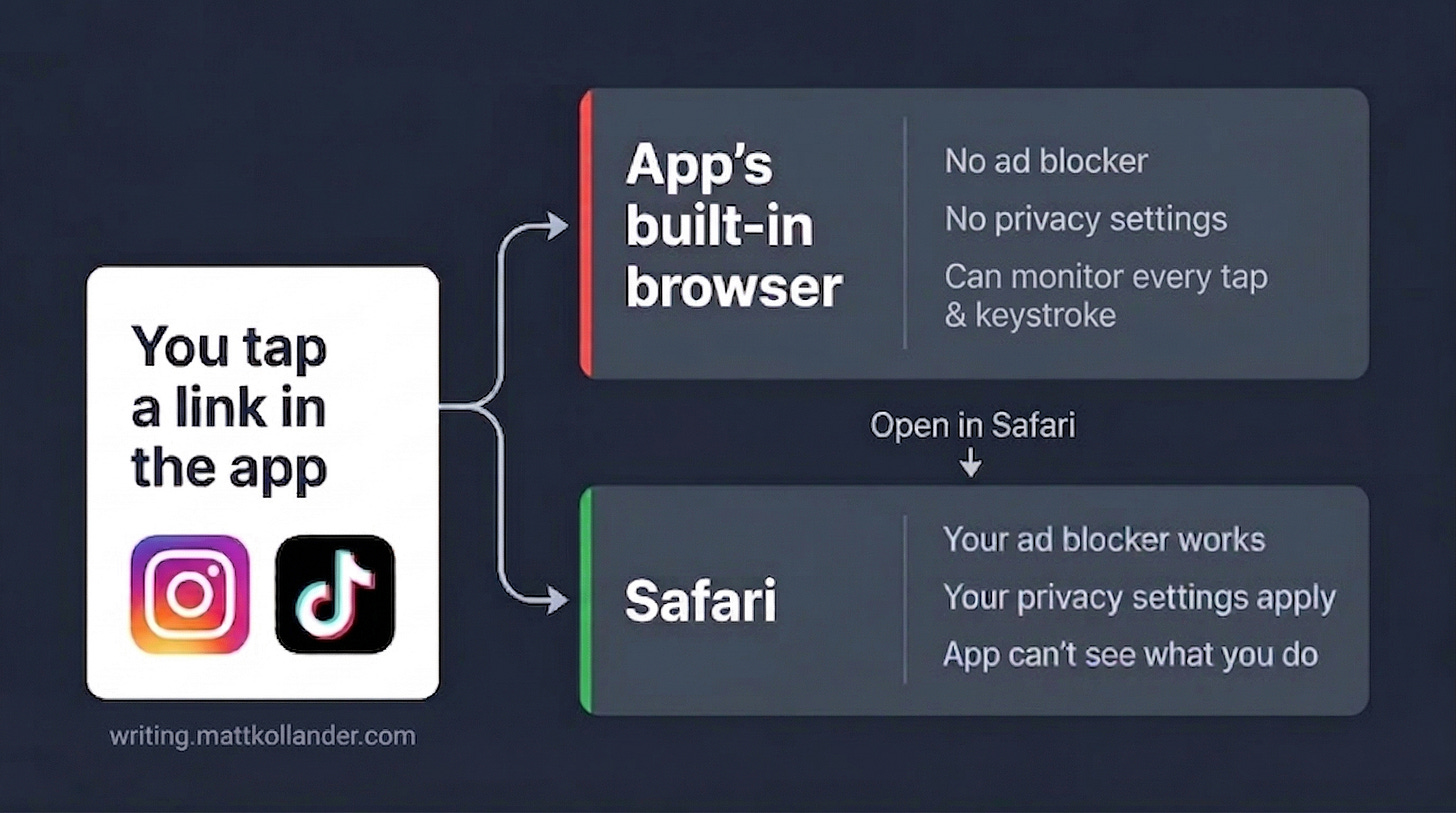
And when you tap a link inside Instagram or TikTok, the page doesn’t open in Safari or Chrome. It opens inside the app’s own built-in browser. In 2022, a former Google engineer turned privacy researcher named Felix Krause published what he found when he looked inside those browsers. Instagram’s browser injects Meta’s tracking script into every website you visit through it, monitoring every tap on buttons, links, and images. TikTok’s browser was worse. It subscribed to every keystroke using JavaScript commands that record every key you press. Krause called it the equivalent of installing a keylogger on third-party websites. If you’ve ever entered a credit card number, a password, or your address on a page that opened inside TikTok or Instagram, the app had the technical ability to see it and record it.
If a hacker did this, they’d go to prison. TikTok does it legally because you agreed to their Terms of Service when you installed the app. You did read those, right?
Krause caught them. But Apple provides a tool that lets apps run injected code in a way that external analysis tools can’t see. If TikTok stopped monitoring keystrokes, we’d have no way to verify it. If they didn’t stop, we’d have no way to detect it. Whether these practices continue in 2026 is unverifiable by design.
Your phone’s privacy settings? Your ad blockers? None of them work inside that built-in browser. The app controls it completely.
You might think cookies are evil and useless. But some of those tracking files do something more important and useful than following you around. They keep you logged in.
That’s why you can close your laptop, open it tomorrow, go to Gmail, and you’re already signed in. A cookie did that. +100 for convenience.
The downside is that anyone who has a copy of that file can get into your account. No password needed. No two-factor authentication challenge. The cookie is the key.
There’s a growing industry built on stealing those files from hundreds of thousands of computers at once. The tool is called an infostealer, a virus that runs silently in the background, rummaging through your browser’s cookie storage and sending everything to a server. The virus is sold as a subscription. About $200 a month. One version called Lumma infected 394,000 computers in two months. Each victim’s stolen data sells for five to twenty-five dollars on underground marketplaces. Do the math: 394,000 victims at ten dollars each is $3.9 million with minimal effort.
They buy your stolen login, load it into their browser, and they’re in. Your email. Your bank. Your browsing history. Everything.
In 2021, someone bought a stolen cookie for $10 on an underground marketplace called Genesis. That cookie belonged to an employee at Electronic Arts, the company that makes FIFA, Madden NFL, The Sims, and Star Wars games. They imported the cookie, got into EA’s internal Slack, talked their way deeper, and stole 780 gigabytes of data including the source code for FIFA 21. Ten dollars. No password. No hacking. Just a cookie.
The FBI shut down Genesis in April 2023. They called it “Operation Cookie Monster.”
The 2025 Verizon Data Breach Investigations Report found that 54% of ransomware victims (ransomware is an attack that locks your files and demands payment) had their stolen credentials sitting on underground marketplaces before the attack even hit. The cookie was already stolen. The attacker was already inside.
The system isn’t broken. It’s working exactly the way it was set up to work. Just not for you.
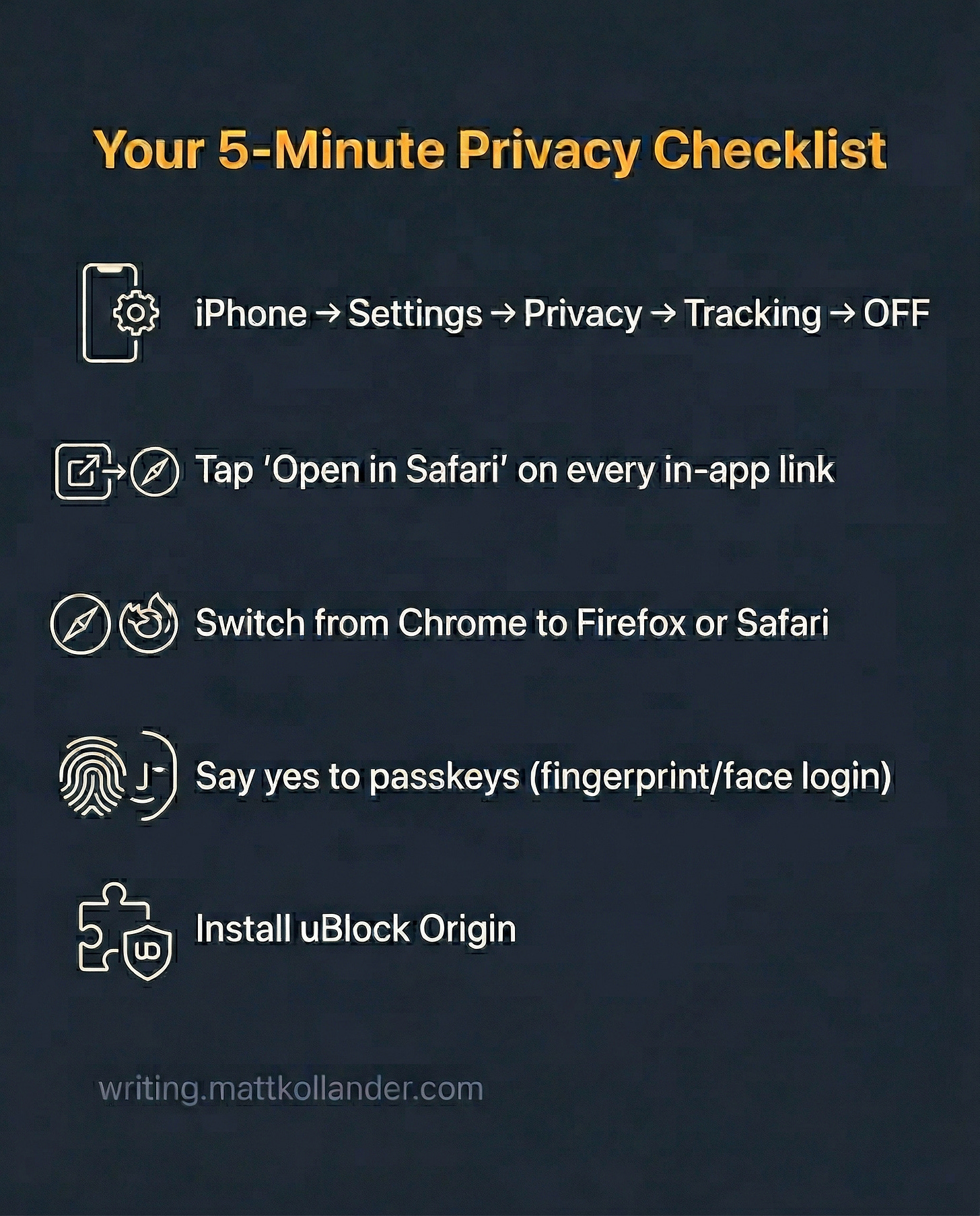
The confusion is deliberate. The five-click “Reject All” process, the tiny gray text, the in-app browser that ignores your settings. All designed to make you give up. So here’s how to fight back.
Five things. Most of them take less than a minute.
1. On your iPhone: Go to Settings, then Privacy & Security, then Tracking. Turn off “Allow Apps to Request to Track.” This is the single most effective privacy setting on any device. About two-thirds of people who see the prompt say no. Don’t be part of the other third. If you have a Google phone or Samsung, this setting doesn’t exist. Google doesn’t require apps to ask. So go buy yourself an iPhone. Message not sponsored by Mr. Tim Cook.
2. When you tap a link inside Instagram, TikTok, or Facebook: Don’t browse inside the app. Look for the small button that says “Open in Safari” or “Open in Browser.” Tap it every time. One tap gets you out of the app’s surveillance browser.
3. On a computer: Switch from Chrome to Firefox or Safari. Chrome is the last major browser that allows tracking by default. Google made $265 billion from advertising in 2024. Those trackers are what the advertising runs on. If you use Firefox, install a free extension called uBlock Origin. If you use Safari, install uBlock Origin Lite from the App Store. Same developer. Same idea.
4. Use passkeys when offered. When a website lets you log in with your fingerprint or face instead of a password, say yes. A passkey is a login locked to your specific device and the specific website. It can’t be stolen, guessed, or reused. About half the top 100 websites now support them.
5. Know the system. In Europe, the law requires websites to ask before tracking you. In the United States, there is no federal law that does the same thing. That banner isn’t designed to protect you. It’s designed to make you feel like you had a choice.
My dad had no idea that playing guitar for a guy in a bear costume would have anything to do with your browser history. But here we are.
Every week, same bit. The bear asks nicely for a cookie. Andy screams NO. Door slam. Audience laughs.
Fifty-seven years later, the bear won. There are thousands of them now. They don’t wear costumes. They don’t ask nicely. They sit inside your apps, your browser, your phone, quietly collecting everything. And unlike Cookie Bear, they don’t take no for an answer.
But Andy Williams understood something Silicon Valley doesn’t: sometimes the right answer to “Can I have a cookie?” is to slam the door in a bear’s face.
🖖
Sources
“The Andy Williams Show,” Wikipedia. Cookie Bear played by Janos Prohaska, 1969 season. https://en.wikipedia.org/wiki/The_Andy_Williams_Show
C.D. Tavares, “Origin of the Cookie Monster,” Multicians.org. IBM 2741 Selectric terminals at 134.5 baud. https://multicians.org/cookie.html
ScienceDirect (2025), “Large-scale web tracking and cookie compliance.” 43% non-compliance post-rejection. https://www.sciencedirect.com/science/article/pii/S1084804525001195
Infosecurity Magazine, “800% Rise in Infostealer Credential Theft.” https://www.infosecurity-magazine.com/news/staggering-800-rise-infostealer/
Microsoft Security Blog, “Lumma Stealer.” 394,000+ infections, 2,300 domains seized. https://www.microsoft.com/en-us/security/blog/2025/05/21/lumma-stealer-breaking-down-the-delivery-techniques-and-capabilities-of-a-prolific-infostealer/
Intelligence Security, “What Are Stealer Logs?” $5-$25 per log. https://intelligencesecurity.io/en/blog/what-are-stealer-logs-infostealer-malware-guide/
HTTP Archive Web Almanac 2025, Cookies chapter. https://almanac.httparchive.org/en/2025/cookies
Google, “How Google uses cookies.” https://policies.google.com/technologies/cookies
ACM WWW 2023, “Facebook Web Tracking.” Meta Pixel on 18.4% of websites. https://dl.acm.org/doi/fullHtml/10.1145/3543507.3583311
Felix Krause, “Instagram and Facebook in-app browser tracking.” Aug 2022. https://krausefx.com/blog/ios-privacy-instagram-and-facebook-can-track-anything-you-do-on-any-website-in-their-in-app-browser
Felix Krause, “InAppBrowser.com.” Aug 2022. https://krausefx.com/blog/announcing-inappbrowsercom-see-what-javascript-commands-get-executed-in-an-in-app-browser
TechCrunch, “FBI seizes Genesis Market.” https://techcrunch.com/2023/04/05/fbi-genesis-market-seized-stolen-logins/
Adjust, “ATT opt-in rates 2025.” https://www.adjust.com/blog/att-opt-in-rates-2025/
IAB Europe, Transparency and Consent Framework v2.3. https://iabeurope.eu/transparency-consent-framework/
Mobiloud, mobile traffic 60.5%. https://www.mobiloud.com/blog/what-percentage-of-internet-traffic-is-mobile
Mobiloud, 88% app time. https://www.mobiloud.com/blog/mobile-apps-vs-mobile-websites
UPenn / Big Data & Society. ~18 SDKs per app. https://pricelab.sas.upenn.edu/events/super-sdks
HP Wolf Security, EA breach via Genesis Market cookie. https://threatresearch.ext.hp.com/tracing-the-rise-of-breaches-involving-session-cookie-theft/
Verizon 2025 DBIR. 54% pre-attack credential exposure. https://www.verizon.com/business/resources/reports/dbir/
Descope, “2025 FIDO Report.” 48% passkey support among top 100 sites. https://www.descope.com/blog/post/2025-fido-report
Alphabet Inc., Q4 2024 Earnings (SEC Form 8-K). Google advertising revenue $264.6B in fiscal year 2024. https://www.sec.gov/Archives/edgar/data/1652044/000165204425000010/googexhibit991q42024.htm